Update: As pointed out to me by Eric Mann, the video is actually for CVE 2016-10033 (which was patched in WordPress 4.7.1), but the vulnerability I’m describing is CVE 2017-8295. Details about CVE 2016-10033 can be found here.
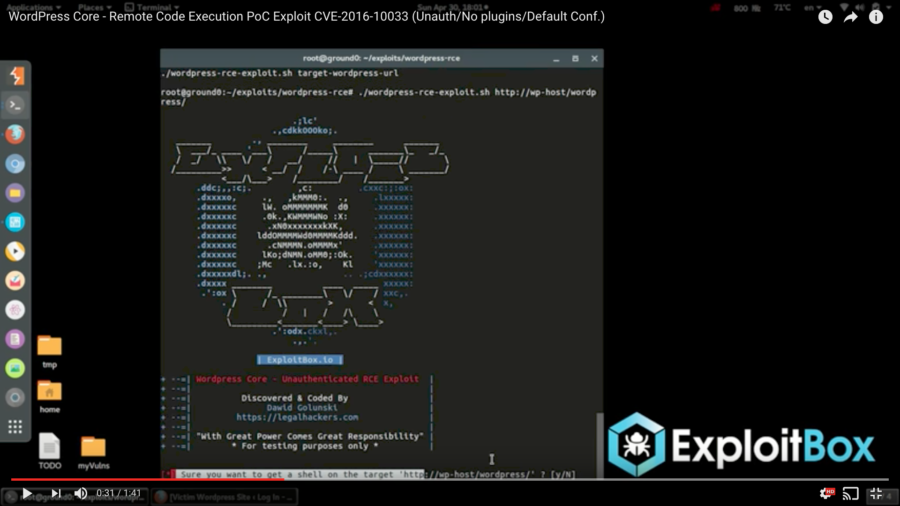
A few days ago, a YouTube video was passed around a few Slack teams I’m a member of showing a proof of concept of an unauthenticated remote code execution vulnerability in WordPress core (in other words, a way for people to execute arbitrary code on your server, which is obviously bad). The video, posted by Dawid Golunski of Legal Hackers, purported that the vulnerability was exploited against a clean installation of WordPress with no plugins and only the default configuration.
This morning, Dawid’s new site, ExploitBox, posted details about the vulnerability. In short, by spoofing a request’s “Host” header, it’s possible to trick WordPress into sending a password reset email with a return path pointing to a domain you control.
The author goes on to hypothesize that if an attacker were to first overload the target’s inbox with large messages (effectively filling it to the point that it couldn’t hold more messages), this would cause the mail host to “bounce” (reject) the message, returning it to the sender (the attacker). Assuming the returned email contained the body of the original message, the attacker now has the link that will allow them to change the user’s password.
Fortunately, this can easily be prevented with good server configuration — explicitly setting the server name in the virtual host configuration eliminates any ambiguity, and renders this attack vector benign. I’ve put together this simple Bash script to check if a site is vulnerable and released it for free on GitHub.
Where’s the lesson in this?
What can we learn from the chatter around this vulnerability, though? Keeping WordPress secure can be difficult.
If you’re running your own web server, it’s important to make sure you stay on top of these things; tools like WPScan can be invaluable for making sure your WordPress instance is locked down. Subscribe to the WPScan Vulnerability Database to make sure you know about the latest reported vulnerabilities, and ensure that you’re regularly updating core, themes, and plugins. On the system end, you should be logging into your server at least once a week and making sure that PHP, MySQL, Apache or Nginx, and anything else you rely in is patched, as well as the operating system itself. Keeping a server secure and up-to-date isn’t impossible, but it’s also far from “set it and forget it.”
What happens if you don’t want to have to run and maintain your own server? What if you’re a publisher who just wants to know you’ll be protected? That’s where the idea of managed hosting comes in: companies like Liquid Web (disclosures: I currently work for Liquid Web, and several of these are affiliate links), SiteGround, WP Engine, and Pantheon are able to handle the security and updating of your servers + WordPress sites, automatically!
In fact, that’s one of the reasons I chose to join Liquid Web: Chris Lema’s goal is to make managed WordPress hosting from Liquid Web a no brainer, and he’s enlisted Andrew Norcross, Brian Watson, and myself to make that happen. We’re building tools to make keeping WordPress secure without compromising usability and making web publishing even easier.
Take the plugin visual comparison testing, for instance: when a plugin update is available, Liquid Web is able to automatically spin up a new environment, test the plugin update, and alert you if it changes anything on the front-end of your site. No more worrying that an update will wipe away your settings or break your site! The feature can be disabled, if you’d prefer, but for publishers who want to know their sites will work, this is a huge step towards publisher confidence.
The vulnerability discussed at the top of this post is far from the only one out there in the wild, and while WordPress is considered to be quite secure, a platform running behind over 25% of the web is a big target for attackers. One of the easiest things you can do to bring yourself peace of mind (and reduce your maintenance costs) is to trust your site’s security to a managed host like Liquid Web.



Leave a Reply